Inability to Meet Compliance-Driven Penetration Testing Requirements

The Challenge
Most frameworks like ISO/IEC 27001:2022, PCI DSS v4.0, SOC 2, NZISM, and NIST SP 800-53 now require annual or post-change penetration testing. Many New Zealand-based organizations lack local providers who understand both the technical depth and compliance mapping required
Our Solution
Audit-ready penetration testing aligned to ISO 27001 Annex A.8.8, NZISM Sections 17–18, and PCI DSS Req. 11.4
Tailored test plans for your regulatory framework (GDPR, HIPAA, SWIFT, APRA CPS 234)
Local NZ presence + deep familiarity with IAF MD26, NZ Privacy Act 2020
Final report includes executive summary, CVSS risk scoring, remediation roadmap, and compliance control traceability
Legacy Security Testing is Not Keeping Pace with Modern Threats
The Challenge
Traditional penetration testing does not simulate modern threats such as AI-enabled exploits, LLM prompt injections, cloud misconfigurations, or quantum-vulnerable cryptography.
Our Solution
AI-driven exploit path generation using GPT-based tools
Red and Purple Team simulations using real-world attacker tactics
Quantum cryptographic readiness audits for TLS, PKI, and crypto agility
Secure testing for LLMs and ML models (prompt injection, inference manipulation)
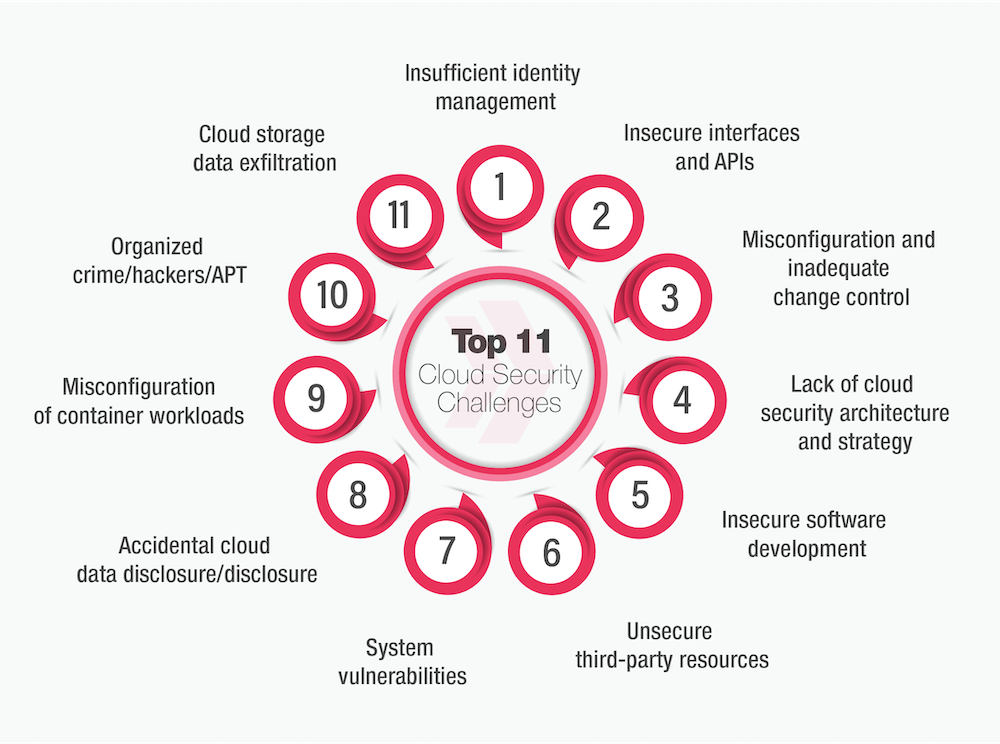
Security & QA Testing Are Disconnected in Modern SDLC
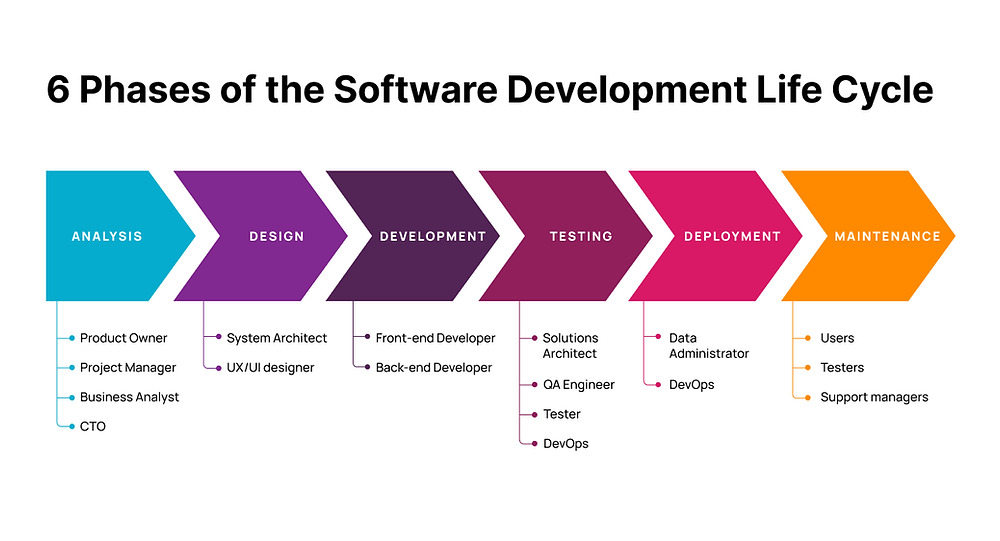
The Challenge
Many businesses operate DevOps pipelines with no integration between security testing and software QA. This results in insecure deployments, delayed compliance checks, and siloed feedback loops.
Our Solution
✅ Integrated DevSecOps pipelines with automated DAST, SAST, IAST tools
Testing-as-Code, Secrets Detection, API fuzzing built into CI/CD
Secure software testing across performance, regression, API, UAT
SDLC alignment with ISO 27001 A.5.36, OWASP ASVS, and Privacy-by-Design
Lack of Local Cybersecurity Testing Providers With Compliance Focus

The Challenge
Most frameworks like ISO/IEC 27001:2022, PCI DSS v4.0, SOC 2, NZISM, and NIST SP 800-53 now require annual or post-change penetration testing. Many New Zealand-based organizations lack local providers who understand both the technical depth and compliance mapping required
Our Solution
Audit-ready penetration testing aligned to ISO 27001 Annex A.8.8, NZISM Sections 17–18, and PCI DSS Req. 11.4
Tailored test plans for your regulatory framework (GDPR, HIPAA, SWIFT, APRA CPS 234)
Local NZ presence + deep familiarity with IAF MD26, NZ Privacy Act 2020
Final report includes executive summary, CVSS risk scoring, remediation roadmap, and compliance control traceability
Lack of Retesting, Validation, and Ongoing Risk Monitoring

The Challenge
Too many firms conduct one-time penetration tests without follow-up remediation testing or attack surface monitoring—leaving unresolved risks.
Our Solution
All plans include retesting and validation cycles
Optional monthly attack surface monitoring (shadow IT, exposed APIs)
Continuous improvement dashboards, secure recheck scheduling
Support for integrating test results into GRC/trust center tools
Complexity of Emerging Tech (AI, Blockchain, IoT, Quantum)
The Challenge
Modern systems are evolving—AI/ML, IoT, Blockchain—and legacy testing methods are not designed for these stacks.
Our Solution
✅ AI/LLM penetration testing for privacy leakage, prompt injection, logic bypass
Blockchain smart contract security validation
IoT endpoint attack simulation, firmware testing, and MITM protection
Threat Modeling as Code (TMaaC) for complex architectures