Zero Trust Architecture Design & Validation
What is about?

Zero Trust eliminates implicit trust in your networks, workloads, and users. Effective Zero Trust implementation requires architectural planning, segmentation enforcement, and validation through adversarial simulation—not just policy creation.
What we can offer
End-to-end Zero Trust reference architecture design
Microsegmentation enforcement across VLANs, K8s, and SD-WAN
Identity & access modeling (SSO, MFA, JIT, PIM, ABAC/RBAC)
Zscaler ZIA/ZPA, Microsoft Entra, Okta policy simulation
Red Team trust boundary validation (e.g., egress routes, bypasses)
Deliverables:
ZTA Architecture Blueprint
Policy Enforcement Matrix
Threat Emulation Report (pre/post ZT implementation)
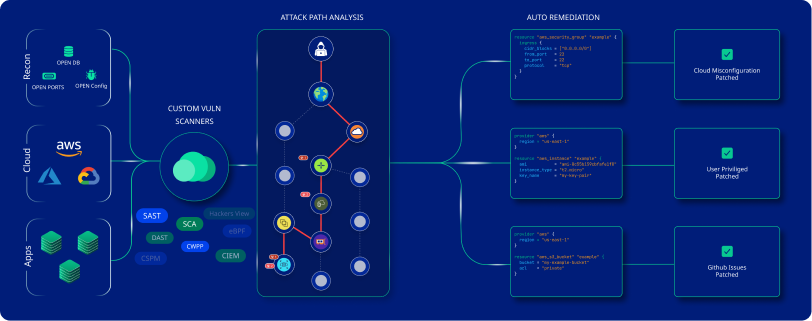
DevSecOps / Secure Software Supply Chai
What is about?
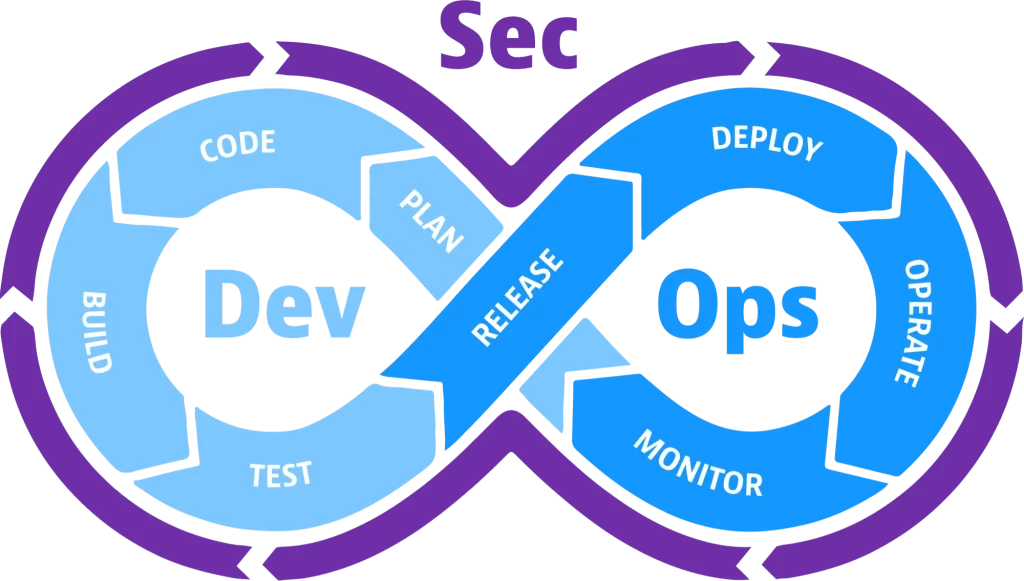
DevSecOps integrates security into every stage of software delivery pipelines—from code commit to production. It is not just about tools, but building resilient engineering practices that detect, prevent, and respond to threats in CI/CD, containers, APIs, and cloud-native apps.
What we can offer
Secure pipeline design: GitHub Actions, GitLab, Azure DevOps
Toolchain integration: SAST, DAST, SCA, IAST, SCA
IaC misconfiguration testing (Terraform, Helm, Kustomize)
Secrets scanning, Git history audit, pipeline secret protection
Runtime protection: eBPF/Falco integration
Deliverables:
DevSecOps Reference Pipeline
Secure IaC Baseline Templates
CI/CD Security Policy Gates
Attestation Reports for Release Audit
Cloud Security Architecture Review
What is about?
Modern cloud environments are highly dynamic and multi-tenant, often suffering from excessive IAM permissions, overexposed storage, or misconfigured security groups. A secure cloud design must enforce least privilege, isolate workloads, and integrate with CSP-native controls.
What we can offer
Cloud misconfiguration testing across AWS, Azure, GCP
IAM privilege escalation analysis and identity graphing
Data security: encryption-at-rest/in-transit, key rotation audit
Container security: K8s PSP, PodSecurityAdmission, runtime threat detection
Integration with Sentinel, SCPs, Azure Policies
Deliverables:
Cloud Security Misconfiguration Report
IAM Attack Path Graph
Remediation-as-Code Recommendations
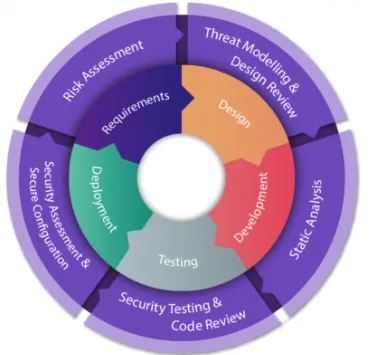
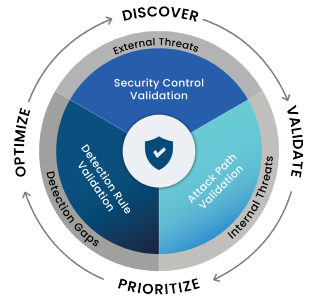
Threat Modeling & Attack Path Engineering
What is about?
Threat modeling proactively identifies risks before systems are built. By decomposing your applications and infrastructure, we can simulate realistic attack paths, validate controls, and prioritize mitigations based on business risk.
What we can offer
STRIDE, LINDDUN, and PASTA-based workshops
TMaaC integration with Git/Jira/CI pipelines
DFD and attack path graph generation using Neo4j or Graphviz
Red Team simulation of modeled threats
Integration with OneTrust, IriusRisk, or custom tooling
Deliverables:
Threat Model Pack (DFD + Threat Tables + Abuse Cases)
Attack Graphs and Exploit Path Maps
Developer-focused Mitigation Sheet
Compliance-Driven Control Validation
What is about?
Security compliance (e.g., ISO 27001:2022, NZISM, PCI DSS, NIST 800-53, SOC 2, Privacy Act) requires technical controls to be implemented and demonstrably effective. Many organizations lack the evidence or mapping required to pass audits or transition between versions.
What we can offer
Mapping control frameworks to technical environments
Evidence generation (logs, configs, scripts, screenshots)
ISO 27001:2022 Annex A gap analysis & implementation
NZISM control test and assurance support
SOC 2 Trust Services Criteria validation and retainer-based support
Deliverables:
Control Validation Matrix
Technical Evidence Bundle
Compliance Readiness Report
Audit Support Response Playbook
AI/ML System Security & Privacy Consulting
What is about?
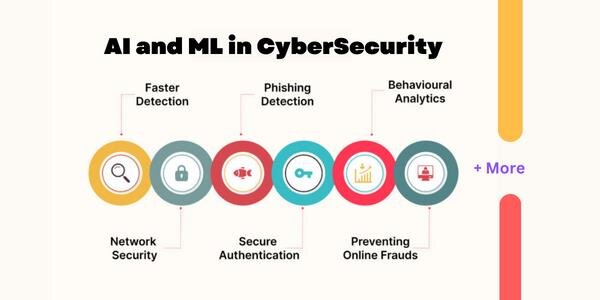
AI/ML systems present unique risks: data poisoning, prompt injection, model inversion, and privacy leakage. Without formal testing, these risks go unnoticed. ISO 27001:2022 (A.5.36) and modern privacy laws increasingly mandate the security and explainability of automated decisions.
What we can offer
Threat modeling of ML pipelines and LLM agents
Membership inference and shadow model attacks
Prompt injection testing for GPT/Claude-based systems
Explainability and fairness audits (SHAP, LIME)
Differential privacy and federated learning security review
Deliverables:
AI System Threat Report
Adversarial Simulation Findings
Risk Treatment Plan
Compliance Mapping (ISO, GDPR, Privacy Act)
Quantum Security Readiness Advisory
What is about?
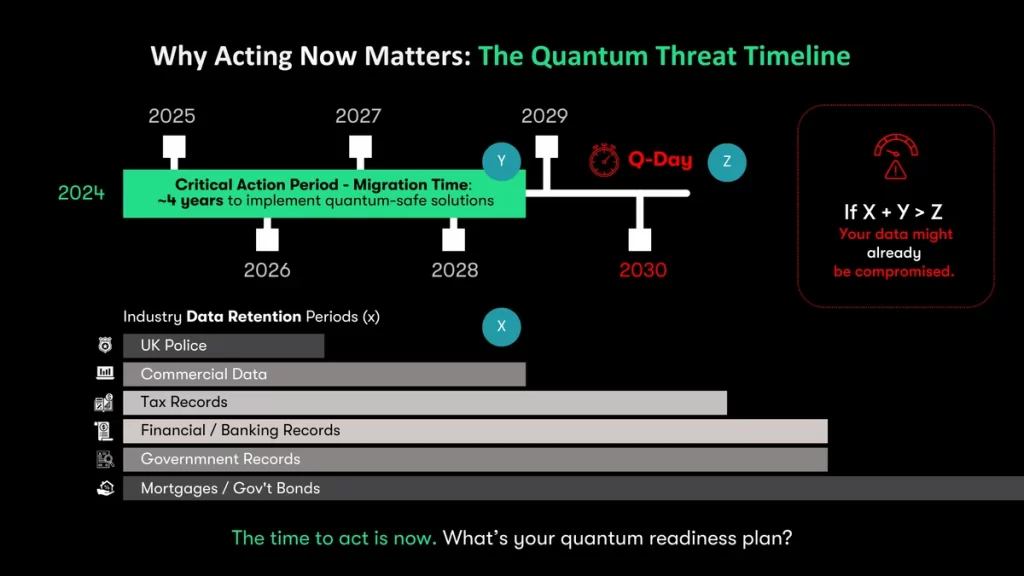
Quantum computing will render RSA, ECC, and other classical cryptography obsolete. The NIST PQC standardization is near final, and proactive organizations must prepare crypto migration plans now to protect long-term confidentiality
What we can offer
Cryptographic inventory across apps, APIs, TLS, and VPN
Key entropy audit and exposure mapping
TLS handshake analysis and downgrade attack tests
Simulation of quantum decryption timing (QUBO modeling)
PQC transition strategy (NIST PQC Round 4 candidates)
Deliverables:
PQC Readiness Report
Crypto Inventory & Exposure Graph
Migration Roadmap
Secure Key Management Architecture (pre/post-PQC)