Penetration Testing for ISO/IEC 27001:2022
What is about?

ISO/IEC 27001:2022 is the international gold standard for information security management systems (ISMS). Organizations certified under the older 2013 version must transition by 31 October 2025 (per IAF MD 26). The 2022 revision places greater emphasis on technical controls, requiring evidence of secure development, threat detection, vulnerability management, cloud security, and data lifecycle protections. Penetration testing is a key tool to demonstrate that these controls are effective in practice.
Challenges Faced
Auditors require technical evidence, not just policies
Cloud, API, and container environments often missed
DevSecOps needs to prove SDLC security effectiveness
What we can offer
Network, API, cloud, and endpoint penetration tests
Threat simulation aligned with A.5.7
Secure code audits aligned with A.5.36
Evidence pack for transition audits
Retesting for remediation closure
Penetration Testing for PCI-DSS v4.0
What is about?

The Payment Card Industry Data Security Standard (PCI DSS) applies to any organization handling credit card data. Version 4.0 introduces new requirements and modernizes testing for both on-prem and cloud environments. Requirement 11.4 mandates annual internal and external penetration testing, and segmentation validation to confirm Cardholder Data Environment (CDE) boundaries.
Challenges Faced
Poor segmentation leads to scope expansion
Shared cloud environments complicate testing
API endpoints often untested in card environments
What we can offer
Internal + external infrastructure testing
CDE segmentation validation
Web/app/API penetration testing
Quarterly vulnerability scans with report submission
Support for ASV report formatting
Penetration Testing for SOC 2 Type II
What is about?
SOC 2 Type II, governed by the AICPA, assesses the operational effectiveness of security and privacy controls over a period of time. It is most commonly used by SaaS and cloud service providers. While pen testing is not explicitly mandated, it is a widely accepted method of validating the Security and Availability Trust Services Criteria (TSC), especially around change control, detection, and data protection.
Challenges Faced
No fixed requirements; depends on scope interpretation
Lack of evidence collection across CI/CD systems
Dynamic infrastructure and frequent code changes
What we can offer
Rolling pen tests during audit window
Security event simulation to test detection
API and SaaS product testing
Integration with DevOps tools for ticket-based remediation evidence
Penetration Testing for NIST SP 800-53
What is about?

NIST SP 800-53 is the US federal standard for information security and privacy controls, used by civilian, defense, and critical infrastructure systems. Penetration testing is required under CA-8 (Penetration Testing) and RA-5 (Vulnerability Scanning) for all moderate and high-impact systems. It’s also foundational to FedRAMP and CMMC.
Challenges Faced
Complex documentation requirements (SSP, POAM, SAR)
Many inherited controls not technically verified
Alerting, SIEM, and access controls often under-tested
What we can offer
CA-8-aligned adversarial testing with threat simulation
Log correlation and event detection validation (AU, SI controls)
System-level exploit testing + FedRAMP tailoring support
Penetration Testing for NZISM
What is about?

The New Zealand Information Security Manual (NZISM) is the official baseline for securing government systems and classified information. It mandates annual and post-change penetration testing (Sections 17.3, 17.4) and system hardening verification (18.2). This is part of the Protective Security Requirements (PSR) for public sector agencies and government-connected vendors.
Challenges Faced
Prescriptive control sets (AppLocker, TLS, patching, SIEM)
Limited internal skills to validate controls technically
Shared infrastructure with private clouds complicates assurance
What we can offer
NZISM-aligned red team or structured pen test
Evidence for AppLocker, Defender, LAPS, TLS, logging, and alerting
Cloud workload validation with secure baseline comparison
Reporting ready for GCDO/DPMC ICT assurance
Penetration Testing for NZ Privacy Act 2020
What is about?

The Privacy Act 2020 modernizes New Zealand’s privacy law and applies to all organizations handling personal information. Under Information Privacy Principle (IPP) 5, agencies must protect personal data with appropriate technical safeguards. Pen testing is an essential way to verify that personal data is not accessible through unauthorized means.
Challenges Faced
APIs and logs may expose PII (including health or financial data)
Consent bypass or retention policy failures are common
Breach notification requirements are strict
What we can offer
API, app, and log testing for unauthorized PII access
Data deletion, retention, and exposure validation
Consent and cookie manipulation testing
Incident simulation to test breach detection
Penetration Testing for HIPPA
What is about?

The Health Insurance Portability and Accountability Act (HIPAA) mandates regular security assessments to protect electronic Protected Health Information (ePHI). Under the Security Rule, organizations must implement technical safeguards and verify their effectiveness—typically through penetration testing and vulnerability scanning.
Challenges Faced
PHI leaks through APIs, URLs, test systems, or logs
Lack of end-to-end encryption and audit controls
Integration vulnerabilities (e.g., FHIR, HL7, 3rd-party EHRs)
What we can offer
ePHI data path mapping and exposure testing
App and network pen tests simulating insider and outsider threats
Role-based access testing (RBAC, ABAC)
Report mapped to Security Rule requirements
Penetration Testing for GDPR
What is about?

The General Data Protection Regulation (GDPR) is the EU’s data protection law, applying to any organization that processes data of EU residents. Under Article 32, data controllers/processors must ensure confidentiality, integrity, availability, and resilience of systems—pen testing is a key tool for this.
Challenges Faced
PII/PHI often exposed via logs, backups, or misconfigured APIs
Consent enforcement may be flawed
Difficulty tracing what data is exposed where
What we can offer
Personal data exposure tests across web, mobile, and APIs
Access control testing (e.g., IDOR, privilege escalation)
Secure deletion, retention, and breach readiness validation
Report aligned to Article 32 and Recital 83
Penetration Testing for NIST Cybersecurity Framework (CSF 2.0)
What is about?
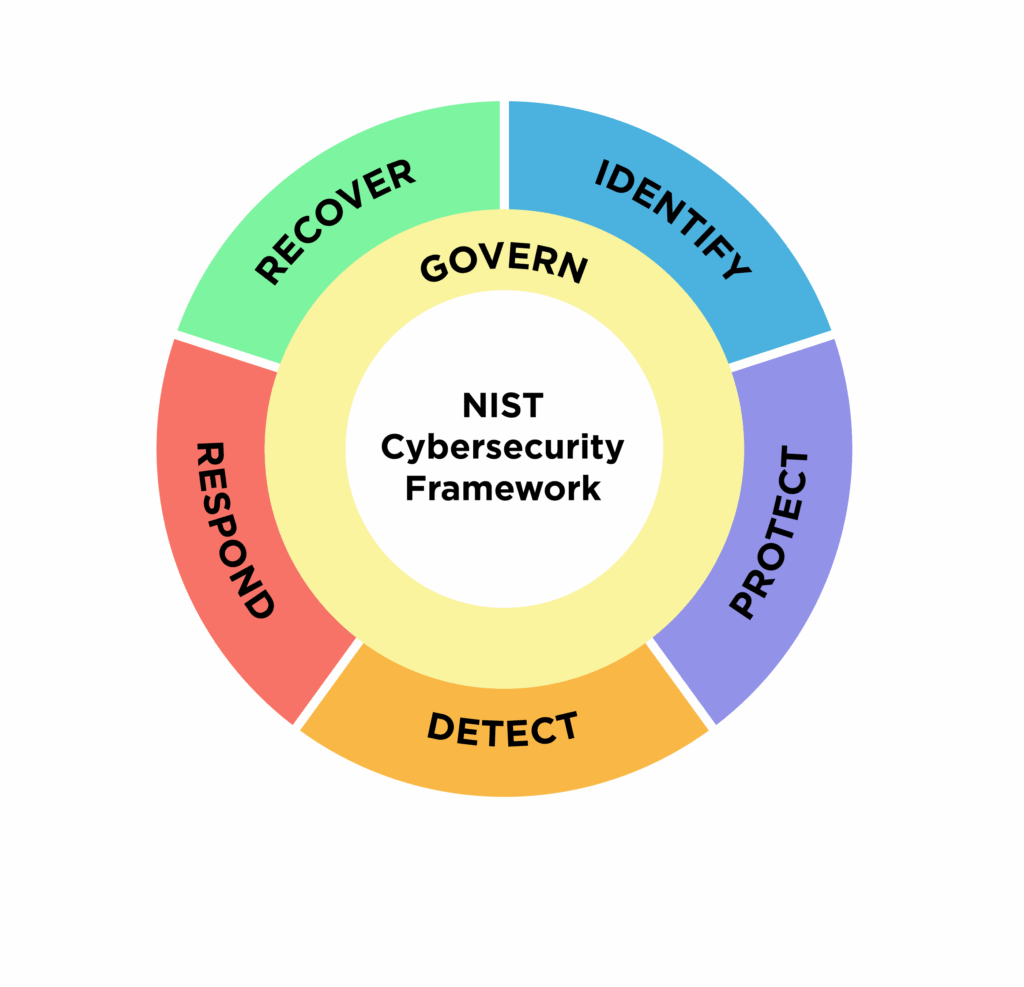
NIST CSF 2.0 is a voluntary but widely adopted framework for managing cybersecurity risk. It defines five core functions: Identify, Protect, Detect, Respond, Recover. Penetration testing supports several outcome categories such as DE.CM-8 (security testing), PR.IP-12 (process validation), and ID.RA-1 (risk assessment).
Challenges Faced
CSF often implemented as a checklist with no validation
No linkage between threats, controls, and risk tolerance
Testing rarely mapped to specific CSF outcomes
What we can offer
Pen testing mapped to CSF categories and outcomes
Real-world attack scenarios tied to business functions
Dwell time, detection, and response simulation
Executive and operational reporting for maturity progression
Penetration Testing for OWASP ASVS / MASVS
What is about?

The OWASP Application Security Verification Standard (ASVS) and Mobile App Security Verification Standard (MASVS) are technical frameworks for testing the security of web and mobile applications. These are often required by secure SDLC programs, regulators, or critical infrastructure sectors.
Challenges Faced
Standard vulnerability scans miss logic flaws (e.g., IDOR, BOLA)
Mobile apps store PII insecurely or fail at SSL pinning
Dev teams deploy code without full security coverage
What we can offer
Full ASVS Level 1–3 and MASVS Level 1–2 testing
Reverse engineering + certificate bypass tests for mobile
Secure coding validation and retesting
Source-code optional review with exploit PoCs
AI-Enhanced Penetration Testing
What is about?

Functional software testing essentially makes sure the software works the way you wanted it to when you set out to develop or purchase a software solution. This approach requires efficiency, so to make the most of our time we’ve incorporated automated testing into our process. Every small update to the app or software won’t require dozens of manpower hours to test before launch.
Test automation helps in reducing regression testing time and cutting down the time to market with significant cost savings on a long-term basis. However, a clear automation strategy and roadmap are key to ensuring the right return on investment on your automation initiatives. With disparate application architecture, multiple environments, third-party integrations and multiple user devices, a standardized and consistent automation approach is needed to ensure high reusability, ease of maintenance and lower upfront costs.
With the experience of advising clients on test automation and architecting their automation journey, SO Test is one of the leading automation testing companies that generates the value you always wanted through test automation. Our test automation solutions support your business objectives by designing an automation strategy aligned with enterprise goals. We carry out a detailed tool evaluation exercise to recommend an optimized tool inventory to suit your needs and budget.
Challenges Faced
Manual pentesting is slow and prone to human bias.
AI systems can be bypassed via prompt injection, data poisoning.
Rapidly evolving threat landscape—new CVEs emerge daily.
API security (broken auth, IDOR, SSRF) often missed.
What we can offer
Hybrid PenTest: Manual testing + AI-driven tools (e.g., GPT-4 for bypass logic)
Full-stack attack coverage: Web, APIs, containers, networks
Authenticated + Unauthenticated paths
Test automation across CI/CD pipelines (DAST + IAST)
Advanced exploit chain generation using NLP models
Deliverables:
CVSS v3.1 scores, PoC scripts, remediation plans
Replayable attack scripts (Burp, Postman, etc.)
Risk-rated technical report and board-level summary
Quantum Security Readiness Audit
What is about?
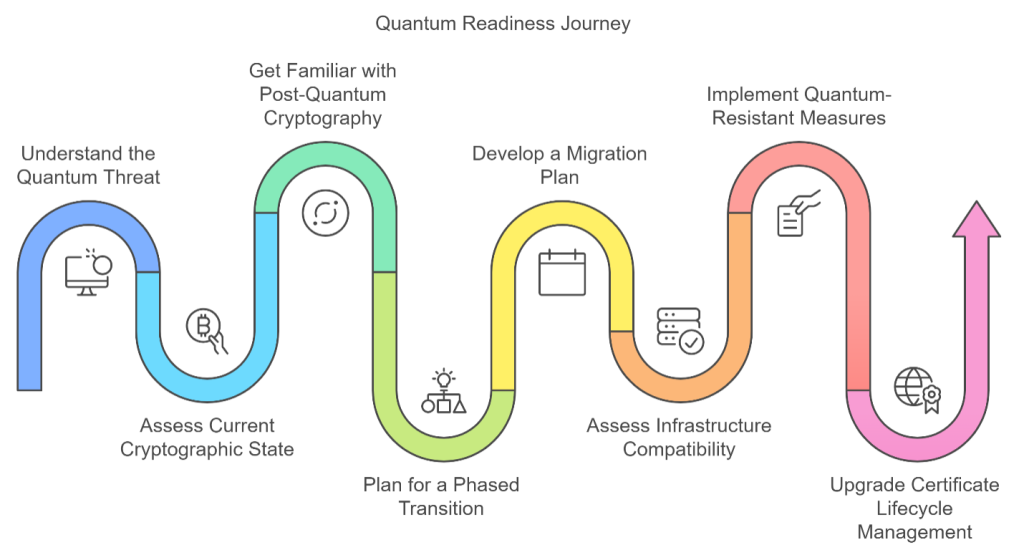
Assessment of your cryptographic systems and infrastructure to ensure resilience against future quantum computing attacks.
Challenges Faced
What we can offer
Inventory of cryptographic use via TLS scans, static code analysis
PQC readiness using Kyber, Dilithium benchmarks
Entropy analysis of key management systems
Quantum simulation testing (D-Wave, Qiskit)
Deliverables:
Crypto Inventory Report
TLS Hardening Guide
PQC Implementation Playbook
Most orgs still use RSA/ECC with inadequate key lengths.
Lack of visibility into where legacy crypto is used.
TLS configurations not quantum-safe.
Compliance teams are unaware of post-quantum cryptography (PQC) requirements (NIST 2024 recommendations).
Secure AI/ML System Testing
What is about?
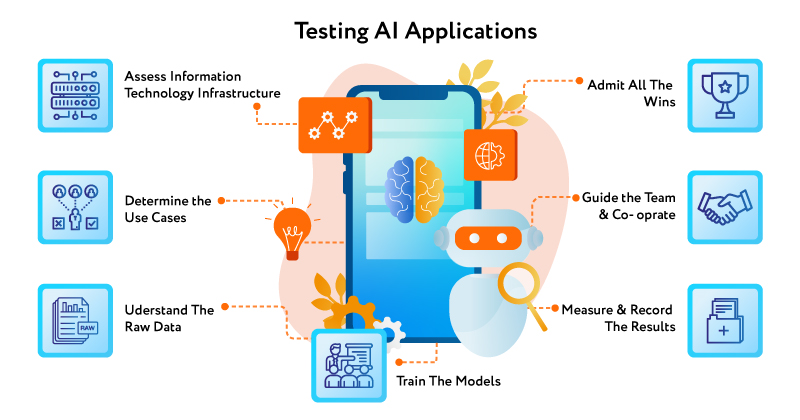
Security evaluation of machine learning systems—including NLP, CV, and predictive models—against attacks such as model inversion, adversarial inputs, and data leakage
Challenges Faced
AI models can leak training data (privacy risk)
Models are black-box to testers
AI security tools are still immature
Regulations like GDPR/HIPAA apply when ML involves PII/PHI
What we can offer
Model inversion & membership inference testing
Adversarial input generation (using FGSM, PGD, TextAttack)
Training data poisoning simulations
ML supply chain security (checking for compromised pre-trained models)
Deliverables:
Risk Matrix (data privacy, integrity, availability)
Attack demos (Colab/Notebook format)
Hardening recommendations (differential privacy, input validation
Threat Modeling as Code (TMaaC)
What is about?
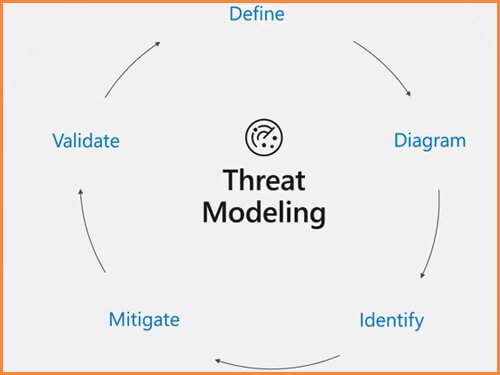
Systematic analysis of architectural risks using structured threat modeling techniques (STRIDE, LINDDUN, Kill Chain), integrated directly into your DevOps workflows.
Challenges Faced
Threat modeling is often skipped or done manually
Developers don’t know how to model threats effectively
Lack of repeatability and traceability
Not integrated with CI/CD or IaC
What we can offer
Threat modeling automation via tools like IriusRisk, PyTM, ThreatSpec
STRIDE per component (network, application, identity)
GitOps integration: threat modeling tied to code commits
Threat graph generation (Neo4j, Graphviz)
Deliverables:
Threat Model Diagrams + Data Flow Diagrams (DFD)
Threat Library per asset/component
Exportable JSON models for Jira or GRC tools
Cloud Security Testing (AWS / Azure / GCP)
What is about?
Assessment of misconfigurations, overly permissive roles, insecure APIs, and identity flaws across cloud infrastructure.
Challenges Faced
IAM roles with wildcard * permissions
Public S3 buckets, exposed Kubernetes dashboards
Poor segregation of Dev vs Prod accounts
Hardcoded secrets in Git, Terraform, or Lambdas
What we can offer
Cloud-native testing: PMapper, ScoutSuite, prowler, Steampipe
IAM attack paths (BloodHound for cloud)
K8s RBAC, pod security policies, container isolation tests
Serverless function misconfiguration checks
Deliverables:
Misconfiguration Reports
Least Privilege Recommendations
Cloud Threat Map
Red Team Operations (Adversary Simulation)
What is about?

Full-scale simulation of persistent threat actors targeting your systems, employees, and supply chain—across physical, social, and digital vectors.
Challenges Faced
EDR evasion is hard without deep attacker knowledge
Organizations struggle to detect lateral movement or C2 channels
No clear way to test defense effectiveness (Blue Team readiness)
What we can offer
MITRE ATT&CK simulation (Atomic Red Team, Caldera)
C2 Frameworks: Sliver, Cobalt Strike, Mythic
Initial access: phishing, payload delivery, USB drops (where allowed)
Purple Team workshops with Blue Team to improve MTTD/MTTR
Deliverables:
Full TTP coverage mapped to MITRE ATT&CK
Detection Engineering Report (SIEM tuning recommendations)
Executive Red Team Summary (with dwell time, detection points
Purple Teaming
What is about?

Purple Teaming is a collaborative cybersecurity exercise where offensive (Red Team) and defensive (Blue Team) experts work together to test, detect, and improve security controls. The goal is not just to “break in,” but to measure and enhance detection and response capability.
Challenges Faced
Lack of visibility into how real-world attacks are detected (or missed)
Delayed response due to siloed offensive and defensive teams
Overreliance on tool-based alerts without proper tuning
Compliance frameworks like MITRE ATT&CK, NIST 800-53 (IR-4, IR-5) require active testing of incident response capabilities
What we can offer
Tactics Based on MITRE ATT&CK
Simulate techniques across Initial Access, Lateral Movement, Persistence, etc.Real-Time Blue Team Collaboration
Help your internal SOC/IR team tune SIEM, EDR, and alert pipelinesPurple Dashboards
Visualize what was detected, how quickly, and what went undetectedReplayable Attack Chains
Use our Atomic Testing scripts to re-run simulations in your CI/CDCompliance Readiness
Evidence package aligned with ISO 27001 A.5.36 and NIST CSF DE.DP, RS.CO
What is about?

Social Engineering tests the human layer of your organization’s security through simulations such as phishing, pretexting, vishing, and physical tailgating. This exposes risks where technology can’t protect you — your people.
Challenges Faced
High click-through rates on phishing emails (20–35% on average)
No way to validate user awareness training effectiveness
Social engineering is required under frameworks like PCI-DSS v4.0 Req. 12.6, SOC 2 (Security Principle), and ISO 27001 A.6.3
What we can offer
Phishing Simulation Campaigns
Credential harvesting, malware drop, spoofed senders, QR-based phishingVishing (Voice Phishing) Scenarios
Live call testing with script loggingUSB Drop Tests
Deliver “infected” USBs with beacon payloads (simulated)Pretext-based Engagements
Simulate impersonation of IT, vendors, or customersMetrics & Training Feedback
Reporting on click rates, response times, and user awareness with improvement plansAudit Reporting
Documented outcomes for audit defense or awareness programs
Social Engineering